Quantum Cryptography and
Physical Layer Cryptography
Article from NICT NEWS 2021 No. 2(Vol. 486)
Researchers: Mikio FUJIWARA, Hiroyuki ENDO
The NICT has been conducting research and development of a technology for a cryptographic communication system that can not be broken even with the most advanced computers in the future, or a quantum cryptography network that ensures information-theoretically secure communication, as well as a technology for building a distributed storage on the network that is also theoretically secure. We have been operating a quantum cryptography network, Tokyo QKD Network, covering an area within 100 km from the center of Tokyo since 2010, and research on spaceborne implementation is also ongoing. This article introduces our efforts and the progress towards global deployment.
Background
RSA and DH are currently the most popular public key cryptography, and are used in cryptographic communication through TLS and digital signatures. However, they are known to be breakable in polynomial time using a quantum computer, and so there is an urgent need to make them stronger. In August 2015, the National Security Agency (NSA) announced a migration to post-quantum cryptography based on a mathematical algorithm resistant to quantum computers. Then, in February 2016, the National Institute of Standards and Technology (NIST) released a plan for standardizing post-quantum cryptography, which is now in its third round as of December 2020. The migration is expected to start in around 2025. However, the post-quantum public key cryptography, which is used to exchange encryption keys, is only computationally secure, which does not guarantee that it will remain unbreakable in the future. Communication that is considered secure today could be broken someday. If genomic information that is encrypted today is decrypted in 30 years, it would cause serious damage, and so it is vital to take measures against information leakage today. A quantum cryptography technology frees us from the threat of decryption and is readily available. However, it has some technical issues such as the transmission distance and key generation rate. It is being implemented in society, along with research for overcoming the above weakness and introducing new functions.
QKD network
Quantum cryptography is a combination of two techniques: quantum key distribution (QKD) that enables sharing a secret key (random number) and Vernam’s one-time pad (OTP) cipher that XORs the transmission data with a random number shared by the sender and receiver bit by bit. Based on the key distribution speed and distance of QKD as shown in Figure 1, with typical optical fiber (having a transmission loss of 0.2 dB/km), a key generation rate of around 100 kbps to 1 Mbps is achievable over a distance of 50 km (transmission loss of 10 dB).
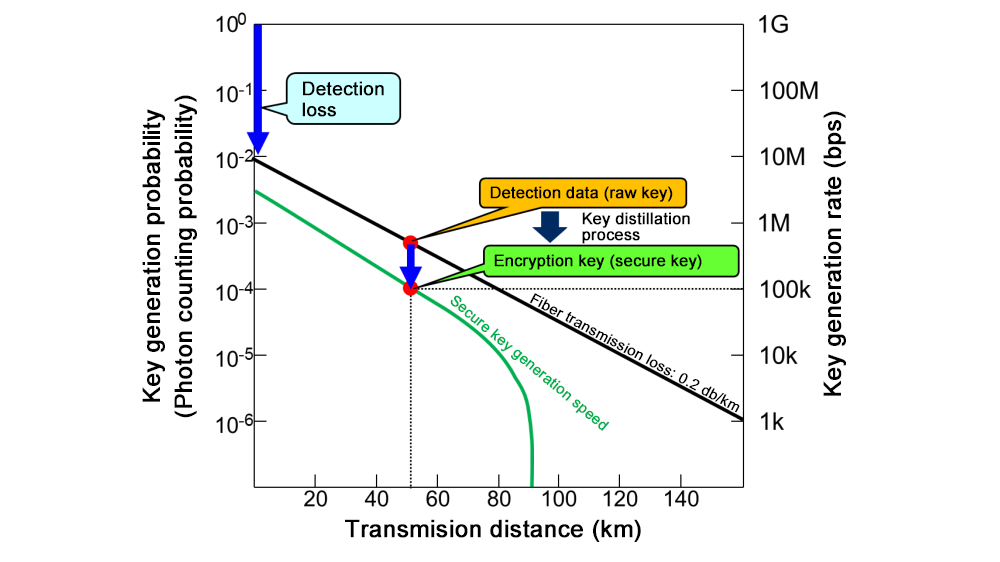
Performance of quantum key distribution
Since the service distance is limited with only a single link, the encryption key information is stored in a trusted node as classical information and the key is distributed by encapsulation relay to extend the key distribution distance, or service area (Figure 2).
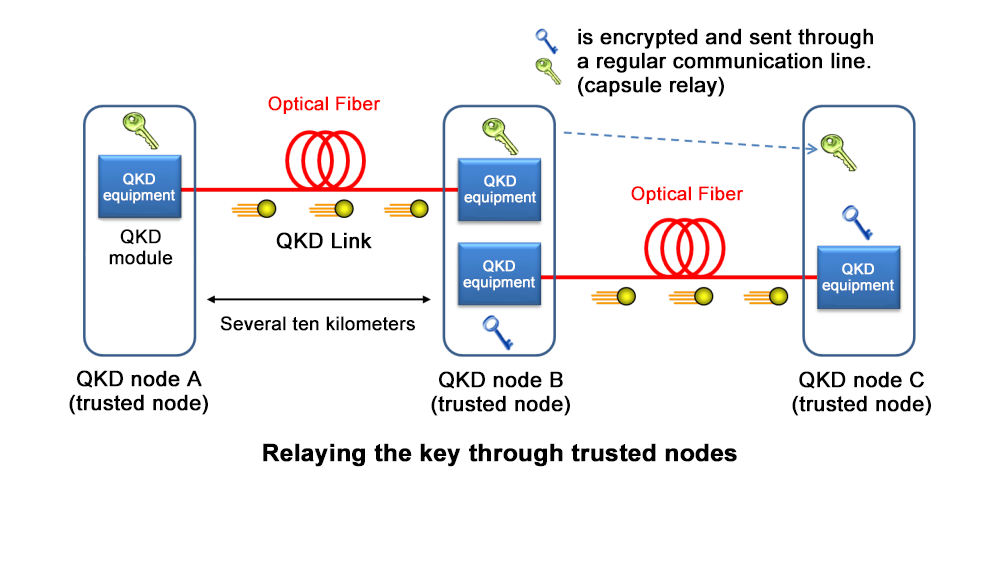
Key relay schematic
QKD links and trusted nodes comprise a network, which is defined as a QKD network. Since 2010, the NICT has been operating Tokyo QKD Network, which was developed to enable reliable key relay even between QKD links of different vendors. The skills acquired through the development led us to establish Y.3800, the first ITU-T recommendation in the field of QKD, and the following series of recommendations, seven in total, demonstrating Japan’s initiative in standardization.
In Europe, the operation of a network with a similar size is starting. China has built a QKD network with a total distance of 2,000 km through key relay between Shanghai and Beijing.
Even though our QKD network is smaller than the Chinese one, it is world-leading in terms of the performance of the QKD equipment, and the reliability and applications of the network.
Quantum secure cloud technology
A quantum secure cloud is defined as a QKD network and a distributed storage built on a quantum cryptography network that enables secure communication using the QKD network (Figure 3). The distributed storage is based on a protocol called secret sharing, which enables information-theoretically secure data storage. Secret sharing converts the original data into several pieces of data called “share” and transmits them through communication secured with quantum cryptography to distant places, where they are stored. The owner of the data can restore the original data by collecting a predefined number (threshold) of shares. If a number less than the threshold of shares is obtained by someone, the information in the original data is never leaked, which is mathematically guaranteed. The concept of secret sharing was first proposed in 1979. However, the secure transmission of shares was merely an assumption. The information-theoretically secure distributed storage of data, which does not rely on hand delivery, became available only after the advent of a quantum cryptography network. In secret sharing, it is also possible to implement a secure computation function that calculates statistical information about the stored data while maintaining its security. This means that secure transmission, storage, and secondary use of data are guaranteed. We are also conducting research and development of various other functions such as user authentication and integrity-ensuring technology. With these technologies, we succeeded in demonstrating the distributed storage of genome analyses, electronic health records (EHR), and biometrics data. Experiments using actual data are underway.
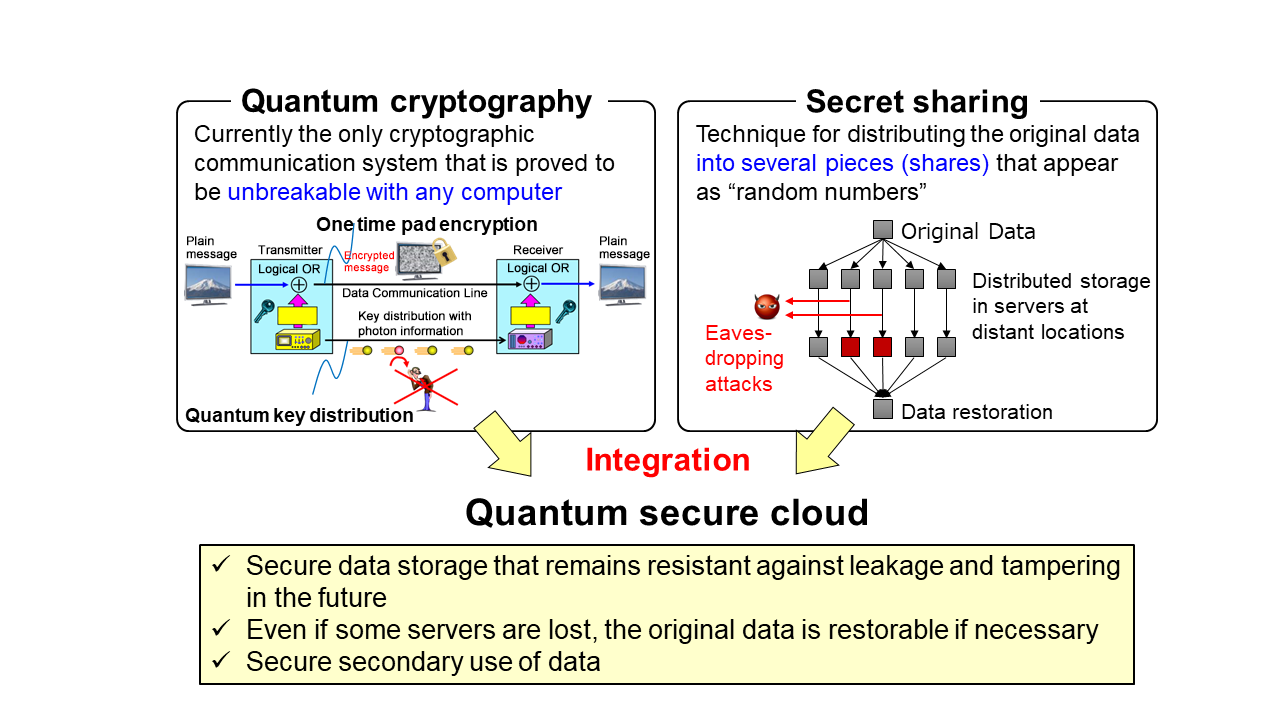
Concept of quantum secure cloud
Future prospects — Towards globalization —
With only a QKD network and a quantum cryptography network using an optical fiber network, it is too costly to cover the whole of Japan, let alone the entire world. Considering the above quantum secure cloud technology as a function like a database, accessing the cloud with an encryption key transmitted by satellite would dramatically expand the service area. Since 2018, the NICT has been participating in the “Research and Development of Quantum Cryptography Technology in Satellite Communication,” a research directly controlled and commissioned by the Ministry of Internal Affairs and Communications, and proceeding with the development of small-satellite-borne equipment and portable ground stations. QKD is designed to be secure even against eavesdroppers by using a quantum computer or quantum memory, in a trade-off with restrictions on throughput. On the other hand, in line-of-sight communication such as that between a satellite and the ground, eavesdroppers in the communication channel can be identified by various means. The attacks available to an eavesdropper can be rationally restricted to passive tapping. We distinguish the technology for securely sharing an encryption key in such a communication channel from QKD and call it “physical layer cryptography.” Research and development is under way on technology for sharing an encryption key at speeds that are orders of magnitude higher than that of QKD. Assuming that either QKD or physical layer cryptography will be used depending on the target, efforts will focus on developing practical technology. It is considered possible to build an information-theoretically secure global network using this technology (Figure 4). We are the only organization in the world which is conducting comprehensive research on a globalization strategy and killer applications, based on feedback from those involved in the NICT with various backgrounds. To achieve social implementation, we will strive to develop this technology into a truly meaningful art, not just a technique for dealing with quantum technology.
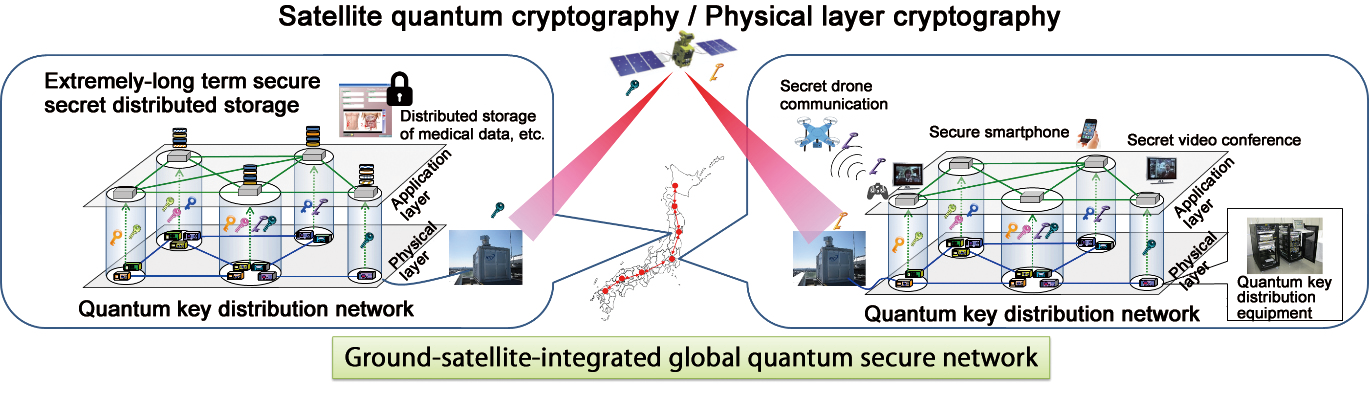
Schematic of ground-satellite integrated global quantum secure-cloud

